Stop Leaking Secrets: The Modern Developer’s Guide to Secret Management

In 2022, Uber was breached when an attacker found hardcoded credentials in a PowerShell script. In 2018, Toyota’s entire customer database was exposed because a developer had hardcoded a database key in a public GitHub repository.
What’s common? A single, stray secret.
In 2025, the pressure on developers is higher than ever. We’re building on complex CI/CD pipelines, using AI coding assistants that are given full access to our systems, and defending against sophisticated software supply chain attacks. The risk of a leak has never been greater.
1. What is a Secret?
A “secret” is anything that should not be public: API keys, database credentials (for all environments, from your local mock data to UAT and customer-facing production), passwords, private encryption keys, and SSH keys.
The core problem is Secret Sprawl. Secrets get scattered. They’re in config files, hardcoded by “lazy” developers, shared on WhatsApp by university teams, or even stored alongside the code that’s meant to use them. Let’s be honest: “Even the best software engineers… might still accidentally reveal secrets.”

And once a secret is out, it’s out forever. “The Internet will remember anything and everything,” so there’s no taking a leak back.
This guide will walk you through the anatomy of a leak, the severe business impact, the developer experience (DevEx) problems this sprawl creates, and the modern toolbox to fix it. Finally, we’ll give you a 10-point playbook to build a secure-by-default culture.
2. The Anatomy of a Leak: Why Secret Management is a Top Priority
Every secret leak follows a predictable, devastating lifecycle.
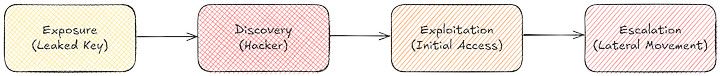
- 1. Exposure: A secret is “snuck out.” It’s accidentally committed to a public repository, left in a public resource, or kept in the front-end code.
- 2. Discovery: Malicious “actors” (hackers) are constantly scanning. It’s not a matter of if they’ll find it, but when. Eventually, they will definitely somehow stumble upon your secret.
- 3. Exploitation: The secret is used to gain “initial access.” Attackers don’t need sophisticated tools; a simple program like Postman can be used to misuse the system by directly communicating to the back end or get direct access to the database. This can lead to extortion (asking for money) or a huge ransomware attack.
- 4. Escalation: The breach doesn’t stop at initial access. This escalation is known as “lateral movement.” The attacker uses that first foothold to move to other systems on the same network layer — for example, getting access to PC1, then running a network scan to find firewall configurations and compromise the entire network.

Source: https://www.youtube.com/watch?v=mXOfblCm93I
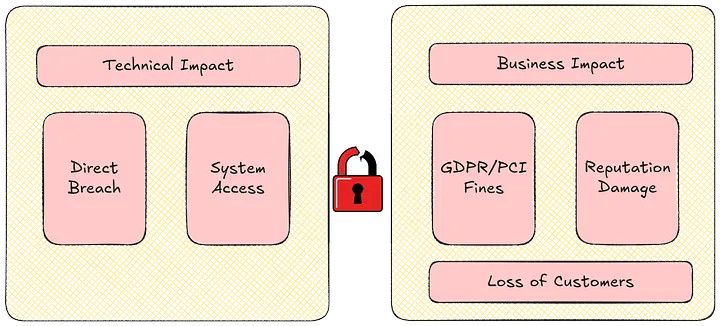
The business impact isn’t just a technical problem; it’s an existential one.
- Compliance Failure: A leak of user data can trigger massive fines from regulations like the EU’s GDPR. If you leak credit card numbers along with their CVVs, you’re in huge trouble with PCI-DSS. These fines are often the primary economic incentive forcing companies to act.
- Financial & Reputational Damage: This is the big one: “reputational damage” and the resulting loss of business. Losing customer trust “can lead to the end of the business.”
- The “Detection Lag” Problem: A DDoS attack is loud; you know about it in milliseconds. A secret leak is silent. Consider this common scenario: a secret is leaked on January 1st, found by a hacker on February 1st, and used for an attack on April 1st. For four months, the company had not a single lead that an attack was coming.
Finally, poor secret management creates a terrible developer experience. A new engineer trying to onboard has to hunt through 10 files for 15 different secrets. When an employee is fired, they might still possess those environmental secrets, forcing the team to waste a huge lot of time manually re-keying every service. It’s a hassle that kills productivity.
2.5. The Inevitable Leak: Your First 5 Minutes (Incident Response)

A proactive when, not if mentality is crucial. When a secret is leaked, every second counts. Your team needs an incident response playbook ready to go.
- Contain: Immediately revoke and rotate the exposed secret. This is the top priority.
- Assess: Determine the blast radius. What systems did this secret have access to? Check logs to see if the secret was used.
- Communicate: Trigger your internal incident response team. Be clear, calm, and factual. Delaying this only makes the problem worse.
- Investigate: How did the leak happen? Was it a code commit? A third-party tool?
- Post-Mortem: After the fire is out, learn from it. Update your pre-commit hooks, improve your scanning, and train the team.
3. A Secret’s Journey: Mapping Environments from Dev to Production
A secret’s value and handling must change as code moves from a laptop to a live server.
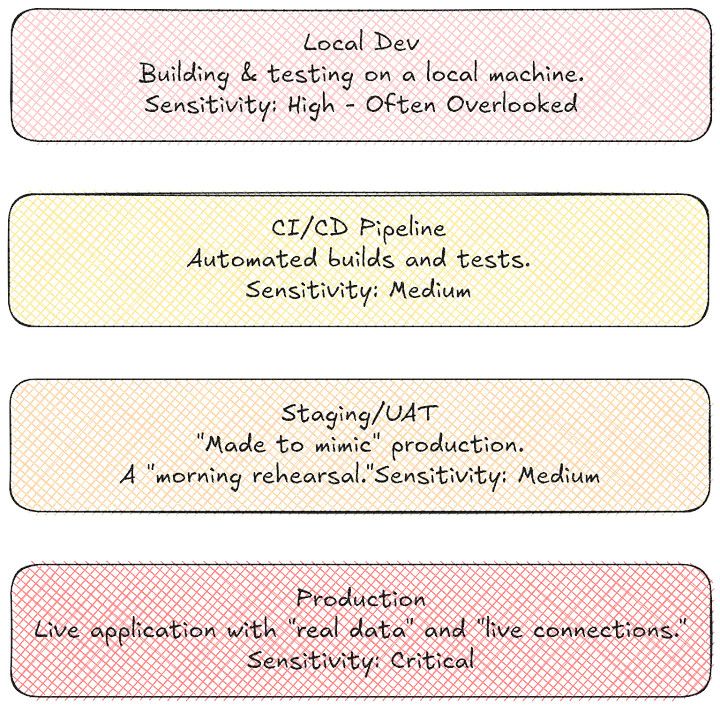
A “who cares?” attitude towards Local Dev is a common and dangerous mistake. A developer’s laptop — if stolen or infected with malware — is a primary attack vector. All local development should still follow best practices like full disk encryption, secure credential caching, and avoiding secrets in your shell history (e.g., history -c or using HISTCONTROL=ignorespace).
There’s one final, often-forgotten stage: Decommissioning. When an application or service is retired, a formal process must exist to revoke all its associated secrets to prevent forgotten, lingering access.
4. The Modern Toolbox: More Than Just a Vault
You can’t solve a modern sprawl problem with old methods. It’s time to upgrade your toolbox.
Part A: Secret Management & Storage
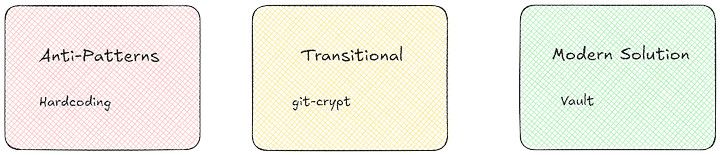
- The Anti-Patterns: Hardcoding, plain .env files in Git, sharing secrets on WhatsApp.
// ANTI-PATTERN: DO NOT DO THIS
const dbConfig = {
host: "prod-db.example.com",
user: "admin",
password: "Password12345!" // Hardcoded secret
};
- Transitional Methods: Encrypted files like git-crypt or platform-native stores like GitHub Actions Secrets (which smartly allows for organizational level and repository level secrets).
- Modern Solution (The Gold Standard): Dedicated Secret Managers.
- Cloud-Native: AWS Secrets Manager, Azure Key Vault, Google Secret Manager. (Warning: These are good, but they create vendor lock-in and risk outages, like the AWS US East 1 data center failure.)
- Platform-Agnostic: HashiCorp Vault (a popular open-source tool you can self-host or buy, acquired by IBM in 2024), Doppler, and 1Password Secrets.
// GOOD PATTERN: Fetching from a manager
import { getSecret } from './my-secret-manager-client';
async function getDbConfig() {
const password = await getSecret("DB_PROD_PASSWORD");
return {
host: "prod-db.example.com",
user: "admin",
password: password // Secret injected at runtime
};
}
Part B: Secret Detection & Monitoring
- Code Scanning: Use static code analysis (SCA) tools to find secrets you’ve already leaked. Examples include TruffleHog, Gitleaks, and SonarQube.

- Platform-Native Scanning: Enable the built-in features on your platform. GitHub’s native scanning, for example, will alert you if it detects patterns matching known secret formats, not just .env files.
- Developer Enablement (Shift-Left): Catch secrets before they’re committed. Use IDE integrations and pre-commit hooks that can be configured to block the commit if the code is not up to standard.
Part C: Secret Injection & Policy Enforcement
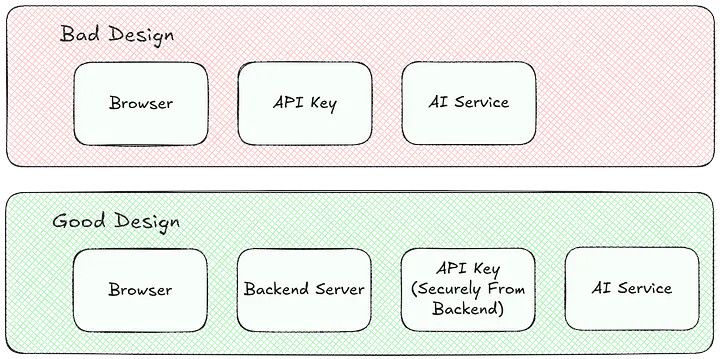
- Injection Patterns: The most secure method is runtime injection, where the app fetches its own secrets when it starts. The worst method is pushing them to the client. Never push a secret to the client browser (e.g., a chatbot connecting to the Gemini/OpenAI API from the front end). That’s giving away your secret in runtime.
- Policy as Code: Use tools like Terraform Sentinel to programmatically enforce rules, like no secret can have a Time-to-Live (TTL) longer than 30 days.
5. Your Secret Management Playbook: 10 Actionable Rules
Here is the 10-point secret management playbook to build a rock-solid, low-friction culture.
- Establish a Single Source of Truth: All secrets live in one, and only one, place (your dedicated manager). It must be treated as the single, authoritative source — “the truth and the only truth.”
- Use Dynamic, Short-Lived Secrets: Don’t use static keys that last for years. Use rolling credentials to generate new secrets daily or maybe half an hour. This keeps the blast radius… really low if a leak occurs.
- Grant Just-in-Time, Least-Privilege Access: Grant just-in-time with least privilege. Don’t give the whole development team… access to the production database. You wouldn’t share a personal secret with your entire 500-person university “WhatsApp group,” and the same logic applies here.
- Automate Secret Rotation: Use automatic secret rotation. This completely solves the hassle of offboarding a developer. With this system, secrets can be rotated so quickly that Half an hour, things are gone.
- Log and Audit All Access: Enable logs and audits on your secret manager. A cybersecurity team should be able to perform a thorough analysis and audit all access logs.
- Sanitize Your Logs: This is a critical, often-missed step. A secret isn’t just in your code; it can easily leak into application logs, error messages, and monitoring dashboards. Implement log sanitization and structured logging to filter or mask all sensitive data before it’s stored.
- Secure Your CI/CD Pipeline: Treat your pipeline as a highly privileged user and never let any unauthorized party get access to the keys used by the CI/CD pipeline itself.
- Embrace Continuous Developer Education: Train new interns or associates on how to code based on the guidelines. This isn’t a one-and-done task.
- Treat Secrets Like Code: Treat your secrets with utmost respect. Arguably, they deserve even more respect than proprietary source code like Tesla’s. A source code leak is a threat; a secret leak is a disaster… in seconds.
- Test Your Defenses: Don’t wait for a real attack. Be proactive by hiring a white-hat security team and doing the simulation runs. This is the same logic as fire drills in offices: assume a breach will happen and make people deal with it in a controlled simulation.
6. Conclusion: From Liability to Enabler
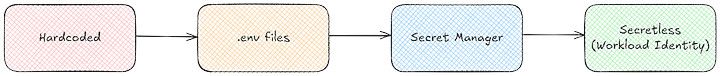
We’ve been on a journey from hardcoding -> environmental variables -> CI/CD variables -> and finally to modern tools like HashiCorp Vault as the “single source of truth.”
This isn’t just about avoiding disaster. It’s about enabling speed. When your secrets are managed, automated, and safe, your developers can move faster.
The next frontier is moving toward secretless architectures, using service-to-service authentication for microservices and encrypting all their communications without a human ever touching a key.
But that’s a journey. The first step is simple. This is your call to action: Look at your code base. If you’re an open-source contributor, take extra caution — your code is public by default.
And for everyone, the first, most practical step you can take right now:
“Don’t forget the .gitignore file.”

This article was also published on my personal blog on Medium