Are DevOps processes secure in nature?
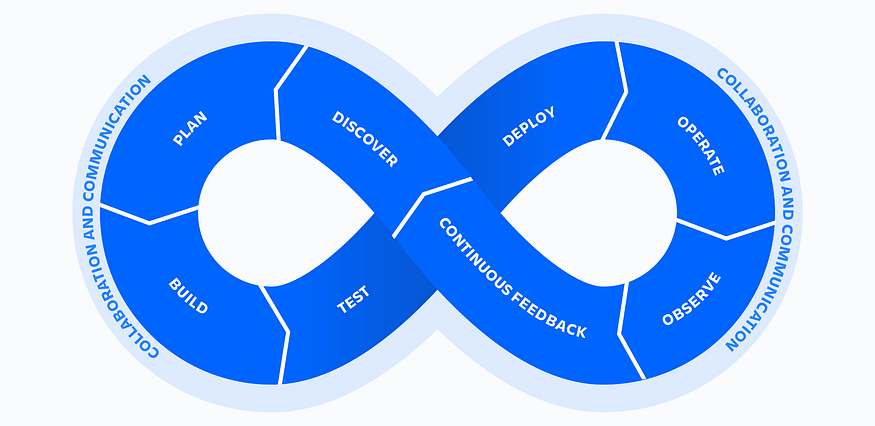
DevOps is essential for delivering software quickly and reliably. By integrating development and operations, DevOps streamlines the software development lifecycle from coding and building to testing and deployment, enabling faster delivery and improved collaboration. However, speed and automation do not guarantee security. Security needs to be intentionally integrated into every stage of the DevOps pipeline to protect applications and infrastructure from evolving threats.

What is DevOps?
DevOps is a convergence of cultural philosophies, emerging tools, and practices that aim to automate and simplify the entire software development lifecycle. This strategy spans everything from original code development to ultimate deployment.
The process evolves through discrete steps:
1.Build Stage
Developers build the codebase and use automation tools (e.g., GitHub Actions, Jenkins, GitLab CI/CD). External libraries and package managers (Gradle, Maven, npm) speed development but introduce supply-chain risk if dependencies are outdated or malicious .
2.Test Stage
Code is extensively tested for bugs and security issues with various methodologies like unit testing, integration testing, performance testing, and security audits. Popular tools among them include Selenium, JUnit, TestNG, and SonarQube.
3.Release Stage
Pre-deployment testing replicates real-world scenarios. Different plans of deployment ensure transitions are smooth:
Blue-Green Deployment : Two different environments ensure that traffic shifting is smooth when updating
Canary Deployment : A subset of users receives the new version initially for security checks
Rolling Updates : Gradual rollout encompasses all users progressively
Major tools are Docker, Kubernetes, Ansible, Helm, and ArgoCD.
In cases where newly deployed versions introduce bugs or vulnerabilities, rollback mechanisms are crucial for restoring previous stable states quickly. Rollback allows teams to revert to an earlier version of the application or configuration without major downtime, maintaining reliability and user trust. Automated rollback strategies can be built into CI/CD pipelines, ensuring that failed deployments trigger instant recovery. This not only minimizes disruption but also strengthens the resilience of DevOps environments.
Under the DevOps model, there are multiple teams coordinating along this lifecycle, typically Quality Assurance and Security teams. They collaborate to automate the development and deployment processes for maximum efficiency and reliability.
Why is DevOps?
The Internet and Software technologies drive the current technology revolution. Companies in industries like healthcare, education, and others require frequent updates of technology. Organizations require faster development, consistency of systems, reliability, and security to compete. DevOps delivers these requirements effectively.

1.Speed Enhancement
DevOps accelerates operations by eliminating human processes, encouraging frequent code changes, automated testing procedures, and increased collaboration among teams.
2.Rapid Delivery Speed
Automated deployment and continuous delivery tools allow for small, frequent, and secure releases. This allows for faster bug fixes and quicker responses to customer requirements.
3.Reliability Assurance
DevOps ensures quality by validating application and infrastructure changes. Continuous Integration & Delivery (CI/CD) auto-validates with testing, so that each change is working and secure, enabling proactive error fixing.
4.Scalability Support
DevOps handles complicated systems well, keeps errors low with automation, views infrastructure as code, and maintains risk low through repeatable and reliable processes.
5.Improved Collaboration
DevOps builds better, more efficient teams based on ownership and accountability models. Developers and operations teams collaborate closely, share workloads, and integrate workflows for best results.
Key DevOps Practices
DevOps practices refer to techniques, guidelines, principles, and tools used in managing software development and deployment. The main objective is to enhance delivery speed and system reliability through automation, monitoring, and collaboration.

1.Continuous Integration (CI)
Developers will typically commit changes to shared repositories. Even minor changes trigger automated tests to run in hopes of catching bugs early.
2.Continuous Delivery (CD)
Continuous Delivery is utilized for automating the release pipeline so that builds are continually tested and deployment-ready.
3.Continuous Deployment
Continuous Deployment goes a step further from the above practice by deploying every approved change automatically into production environments.
4.Infrastructure as Code (IaC)
A DevOps practice that uses machine-readable definition files to manage and provision data center resources like networks, servers, and storage, rather than relying on manual configurations or physical hardware.
5.Configuration Management
Systematic tracking and management of changes to system components, their attributes, and relationships throughout their entire lifecycle.
6.Automated Testing
Executes testing processes in order to deliver high-quality code as well as early detection of issues within the development cycles.
7.Monitoring and Logging
Monitors real-world behavior and identifies problems before they strike.
8.Incident Response and Alerting
Monitoring discovers all types of problems requiring immediate alerting and rapid response to minimize damage.
9.Containerization
Packages up applications in extremely light, transportable containers (like Docker) to deliver consistency across all environments.
10.Environment Automation
Automates uniform development, testing, staging, and production environments to avoid mistakes and maximize efficiency.
Common Vulnerabilities
1. Misconfiguration Vulnerabilities
Misconfiguration is one of the largest DevOps weaknesses, caused by setup, permissions handling, or automation. The speed and depth of these processes may result in such errors. Correct configuration is still of the highest importance; otherwise, attackers may gain administrative privileges and view sensitive data.

IaC Vulnerabilities
IaC tools like Terraform, CloudFormation, and Ansible allow developers to provision and define infrastructure through code. Misconfigurations tend to propagate security weaknesses to whole environments at a rapid pace.
- Overly permissive access controls that set IAM policies with too broad permissions, potentially enabling privilege escalation
- Exposed storage buckets as a result of misconfigured cloud storage (e.g., AWS S3 buckets) becoming public
- Manual drift through changes made manually, causing the deployed infrastructure to diverge from IaC templates and create security blind spots
CI/CD Pipeline Vulnerabilities
The scripted nature of Continuous Integration/Continuous Deployment pipelines can cause misconfigurations to spread quickly from development to production.
- Overly permissive pipeline permissions give CI/CD processes overly broad access, which attackers can use for lateral movement
- Outdated dependencies using software or open-source libraries with known vulnerabilities
- Integrity checks are missing that allow unverified code changes or dependencies to be added without proper verification.
Cloud Services Misconfigurations
Cloud platform complexity, with so many features and configurations, tends to lead to production environment misconfigurations.
Invariant default configurations, such as default admin credentials left enabled, network exposure with public internet access on non-essential ports. Inadequate logging and monitoring make incident detection and response harder. Development settings in production environments leak sensitive information through verbose error messages.
2. Vulnerable Containers
Containerization is at the heart of modern DevOps. From base image creation to container deployment, some disturbing practices can emerge.
- Vulnerable Base Images
Insecure base images are vulnerable base container layers containing known vulnerabilities, malware, or misconfigurations that a hacker could exploit. Due to the layered construction of container images, any security vulnerabilities found in base images are propagated to all derived containers.
- Unpatched Software
Software patches usually provide security patches safeguarding against attack vectors. Failing to apply them results in vulnerable software reaching production environments.
- Privilege Policies
Containers must run under least privilege policies to restrict access. When containers are run with root privileges without certain restrictions, it makes it easier for attackers. Containers need to be given only the privileges needed for their specific use, as too much privilege can leak sensitive information or introduce attack surfaces.
3. Secrets Management Vulnerabilities
Secret management vulnerabilities typically occur through a lack of supervision, insecure infrastructure, or human error in software build and deployment processes. These issues are particularly prevalent in high-stress DevOps environments where security is deprioritized for velocity.

- Decentralized Secret Management
Without dedicated, centralized systems or “vaults” for storing secrets, organizations create disorganized environments that can be exploited.
- Hardcoded Secrets
Hardcoding of sensitive credentials into source code, scripts, or config files is a proven and highly risky mistake.
- Secret Leakage
Accidental leakage of secrets through code, logs, or network traffic can lead to unauthorized access, data breaches, and economic impact.
4. Lack of Shared Ownership
While DevOps culture is teamwork-oriented, having so many people involved can create shared ownership dangers. This creates responsibility ambiguity and system security vulnerabilities that are difficult to fix and costly to companies.
- Blame Assignment
Without shared responsibility, teams will create suboptimal solutions where blame is placed on failure. The “us versus them” mindset between departments erodes security objectives.
- Security as an Afterthought
If security is viewed as a task only for the security team, then it becomes an end-of-process checkpoint rather than being integrated into the development process. End-of-process security testing is time-consuming and expensive, and vital issues might be missed.
5. Over-Automation and Lack of Oversight
Over-automation and poor monitoring in DevOps create security vulnerabilities through interconnected technical and cultural aspects. Urgency to move fast often outweighs security needs, causing teams to automate without proper guardrails, training, or feedback. This sets up systems where defects transmit rapidly and attackers can easily find and exploit vulnerabilities.
6. Automating critical security processes
Teams may automate existing, broken, or inefficient manual workflows without fixing the underlying issues first. This doesn’t eliminate the problems it just makes them happen faster, at scale.
7. Unchecked Deployments
CI/CD pipelines that are too dependent on automation could be deploying code to production too quickly and skipping or avoiding security checks to meet aggressive timelines, arguably increasing the risk of deploying insecure code.
8. Bypass critical reviews
Lacking proper code reviews, quality gates, and constant monitoring, bad code can ship stealthily. The lack of visibility allows bugs and flaws to reside in production.
9. Poor Access Controls
Granting excessive privileges to users or tools increases the risk of widespread damage if compromised. Misalignment between development and security teams leads to security being deprioritized in favor of speed.
DevOps is more effective, but is a security risk if not controlled. It has vulnerabilities like cloud and infrastructure-as-code (IaC) configuration misconfigurations that reveal sensitive data. CI/CD pipelines typically face bad permissions, out-of-date libraries, and missing integrity checks. Container security risks are due to insecure base images and unpulled software, and poor secrets management (e.g., hardcoded passwords and secret exposure) is also under attack. Absence of collective responsibility for security and over-automation also bypasses key security checks and leads to unchecked deployments. These loopholes provide access for the attackers to take advantage of vulnerabilities and gain unauthorized access.

How do attackers take advantage of these loopholes to gain access, and how can they be avoided?
This article was also published on Medium.

References
Here are some resources that I used to craft this article.